Blog
SDPC Midwest Regional School District Training
Join us for the SDPC Midwest Regional School District Training, a focused and interactive event designed for school districts across Illinois, Tennessee and Missouri.

2013 - Pivotal Year in Student Data Privacy
The classroom fundamentally changed in 2013, going from data being held in the four walls to data being shared with third party vendors. This...

Assessments, Threats, Compromises and MORE: MOREnet Cybersecurity Numbers!
For FY25, we visited 16 sites to conduct cybersecurity assessments! These are informal discussions on your best practices, and you will receive a scored assessment and suggestions for improvement.

Five things you can do to mitigate the threat of ransomware attacks:
Ransomware is one of today’s most disruptive cyber threats, but its impact can be greatly reduced with the right defenses. By maintaining reliable backups, enforcing multi-factor authentication, keeping systems patched and updated, training users to recognize phishing attempts, and having a well-practiced incident response plan, organizations and individuals can significantly strengthen their resilience and recover quickly if an attack occurs.

Improving Defenses with Professional Development
Cybersecurity is no longer just the responsibility of the IT department; it’s a collective duty that involves every staff member, teacher, and student....

Cybersecurity Vacation
July and August are typically known as the “summer vacation months” and unfortunately these months also see an increase in cyberattacks. Reduced staffing...

Too Much of a Good Thing – App Overload
Instruction, assessment platforms, reporting systems and parent engagement solutions are all delivered with applications. With so many resources available for use in the...
AI and Guardrails
How do you train staff in best practices when entering data into an AI tool whether it is ChatGPT, CoPilot, etc.?
Data Privacy Agreements: How to Vet a Resource
Several districts have asked for more detail about how to vet a resource prior to entering a request in the Resource Registry. Below...

Using AI for Note-Taking
AI Note-Takers are a great time saver and gaining popularity. The ease of use and ability to produce an agenda and after-action items...

Guide for Developing an Internal Vetting Process
Our data privacy team has created a handy guide to help your district develop a process for ensuring every resource with access to...
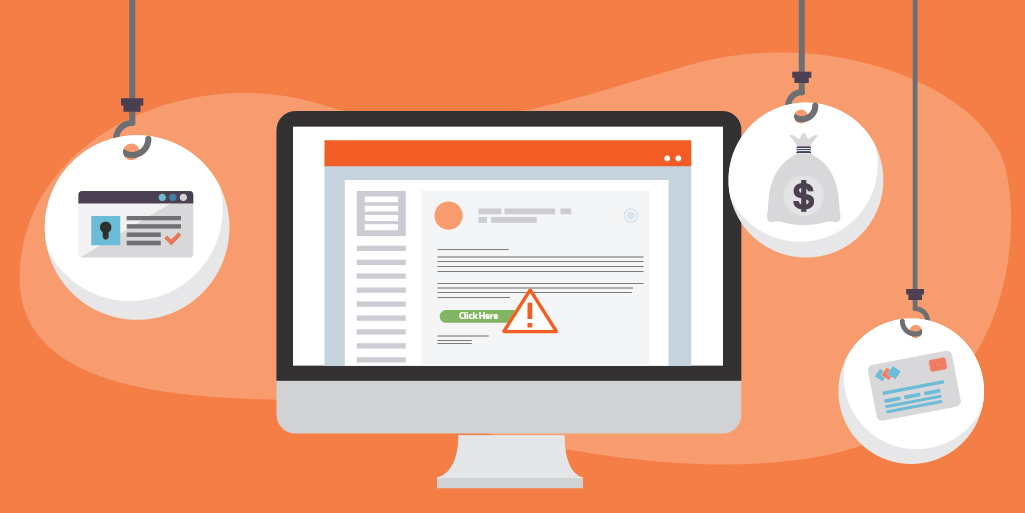
Beware of the 'ishing'
Social Engineering is the use of deception in order to manipulate the victim into performing an action for fraudulent purposes. The bad actor...

CIS Critical Controls Version 8.1
The Center for Internet Security (CIS) has long been respected for it's framework of critical security controls. Released in 2008, it's purpose was...

Data Privacy Day - January 28, 2025: You Have the Power to Take Charge of Your Data
As more data is stored in the cloud or transferred to third parties, how can...

Incident Reporting: Your First Line of Defense
Organizations use layered security to prevent falling victim to a cybersecurity incident. The 3 main elements of layered security require administrative, physical and...

Ring in the New Year with a Cybersecurity Makeover
A new year brings new opportunities. What a great time to review your cybersecurity practices! Evaluate every aspect of your digital life. Check...

Caught in the Web: Common Cyber Crimes
Cyber crime is a broad term that can encompass a wide variety of malicious activity. These attacks can be aimed at networks, businesses...

Salt Typhoon Cyber Attack
The Salt Typhoon cyber attack, conducted by bad actors in China, targeted telecommunication organizations. Major telecom companies were hacked, including AT&T, Verizon, T-Mobile...

'Tis the Season for Holiday Scams
Scammers are especially active during the holiday season. The crooks are taking advantage of the consumer's good cheer, generous nature, and hunt for...

