Blog
16 Billion Passwords Leaked: What to do
Another breach
In June 2025, cybersecurity experts uncovered the largest password leak ever—over 16 billion unique passwords exposed and actively traded on the dark...

Too Much of a Good Thing – App Overload
Instruction, assessment platforms, reporting systems, and parent engagement solutions are all delivered with applications. With so many resources available for use in the...

Reputational Harm from Cyber Incidents
“You don’t want to be on that list.” Cybercrime Magazine’s Paul John Spalding and Steve Morgan, Founder of Cybersecurity Ventures discussed how cyber...

Security Awareness Training is Essential in 2025
As cybersecurity threats evolve, educational institutions remain prime targets, with the human element often representing the weakest link in security. Security awareness training...

Google Resources On The Move!
Heads up teachers, techs and librarians! Two great resources from Google just got new homes and partnerships that are REALLY exciting! ...
AI and Guardrails
How do you train staff in best practices when entering data into an AI tool whether it is ChatGPT, CoPilot, etc.?

Creating a Contact List for Cyber Incident Reporting and Assistance
Cyber criminals continue to organize themselves-- from building scam center office complexes to creating ransomware payment help desks. The more organized, sophisticated and...
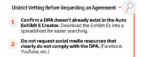
Data Privacy Agreements: How to Vet a Resource
Several districts have asked for more detail about how to vet a resource prior to entering a request in the Resource Registry. Below...

Data Mapping and Inventory: What they are, How important are they, and How to do them.
Effectively managing your data is critical for compliance, risk reduction, and informed decision-making. Data mapping and inventory are foundational practices for any organization...

Cybersecurity and Accessibility
People with disabilities face an increased risk of being a victim of cybercrime due to the lack of tool...

Next-Gen Phishing Training
New AI-tuned phishing attempts are cause for re-evaluation of user phishing training. With AI chatbots able to assist in the generation of email...

The Rise of AI Scams: What You Need to Know to Stay Safe
AI is making scams smarter, faster, and harder to spot. Criminals now use artificial intelligence to create ultra-realistic phishing emails, fake voices, and...

Using AI for Note-Taking
AI Note-Takers are a great time saver and gaining popularity. The ease of use and ability to produce an agenda and after-action items...

Vishing 3.0
Cybersecurity threat trends continue to evolve, but seemingly outmoded threats vectors don’t always go away; sometimes, like in the case of vishing, they...

Tax Season AI-Powered Scams Are Targeting You—Here’s How to Stay Safe
As tax season ramps up in 2025, cybercriminals are leveraging cutting-edge technology to launch their most convincing and costly...

“Wi" Should I Log?
Guest wireless is a convenience to offer visitors. What information should be logged for these connections?
If someone used the...

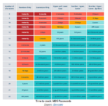
Guide for Developing an Internal Vetting Process
Our data privacy team has created a handy guide to help your district develop a process for ensuring every resource with access to...

Cheap (Cybersecurity) Wisdom
Russell Eubanks in a SANS Institute video “Improve Your Cyber Security Culture” offers the following advice learned from one of his own mentors:...

The Reality of IoT Security : Guests on Your Network
IoT devices and other vendor appliances, while convenient, are often security weak points. They frequently ship with outdated firmware, weak passwords, and even...

Don’t Just “Google it”
“Google” is now a term embedded in our language and s iroutinely used. As with all routines, we may become complacent on how we...
