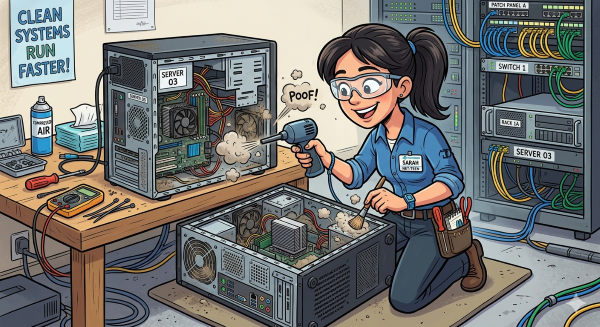
Spring is the perfect time to clean out the dust bunnies from your processes, policies, network closets, devices, and infrastructure. Below is a checklist to assist you with this project.
- Physical Cleaning
- Inspect network closets for added items i.e. boxes, cans, etc.
- Clean room air vents.
- Organize and label cabling.
- Document all changes.
- Audit your hardware and software
- Identify devices nearing end of life.
- Switches, servers, computers, printers, UPS, etc.
- Licenses you are no longer using.
- Software duplication – applications that accomplish the same task or are no longer relevant.
- Ensure software is up to date
- Outdated software is a top vulnerability that is exploited.
- Document all changes.
- Identify devices nearing end of life.
- Accounts and Permissions
- Remove inactive user accounts.
- Apply the principle of least privilege – give users access to only what they need.
- Review AD to ensure users are in appropriate groups/permissions.
- Document all changes.
- Network
- Know your baseline of usage.
- Identify all the devices you need to monitor and how often.
- Scan for rogue WiFi devices
- Consider a SIEM to compile all your logs.
- Are your firewall rules up to date?
- Is your firewall sending response(s) when the original packet is dropped?
- Consider configuring the firewall to drop those packets and not send a response.
- Scan for unauthorized agents.
- Document all changes.
- Network Map
- Review and update.
- Ensure appropriate staff have access to the document.
- Document all changes.
- Backup Systems
- Test Restores.
- Confirm the 3-2-1 backup rule – 3 copies, 2 media types, 1 offsite..
- Document all changes.
- Digital Cleaning
- Delete temp files and cookies.
- Remove unused applications.
- Archive email.
- Document all changes.
- Incident Response Plan
- Dust off the manual and review with the team.
- Are all the contacts correct?
- Are there additional applications or services to add?
- Are there new staff to inform of the plan?
- Document all changes.
- Privacy
- Review your own privacy policies and ensure they align with third party data privacy agreements.
- Review organization wide applications and reduce redundant applications.
- Request student data be deleted if you are no longer using the application or per your policies.
- Document all changes.
- Policies and agreements
- What policies need to be updated?
- Have third party vendors changed such as network assistance, HVAC, cameras, etc.? Do data privacy agreements need to be implemented?
- Document all changes.
Routinely cleaning your network will increase your cybersecurity posture, awareness, and defense. Please contact us if there is anything we can do to assist!
