Blog

Too Much of a Good Thing – App Overload
Instruction, assessment platforms, reporting systems and parent engagement solutions are all delivered with applications. With so many resources available for use in the...
AI and Guardrails
How do you train staff in best practices when entering data into an AI tool whether it is ChatGPT, CoPilot, etc.?
Data Privacy Agreements: How to Vet a Resource
Several districts have asked for more detail about how to vet a resource prior to entering a request in the Resource Registry. Below...

Using AI for Note-Taking
AI Note-Takers are a great time saver and gaining popularity. The ease of use and ability to produce an agenda and after-action items...

Guide for Developing an Internal Vetting Process
Our data privacy team has created a handy guide to help your district develop a process for ensuring every resource with access to...
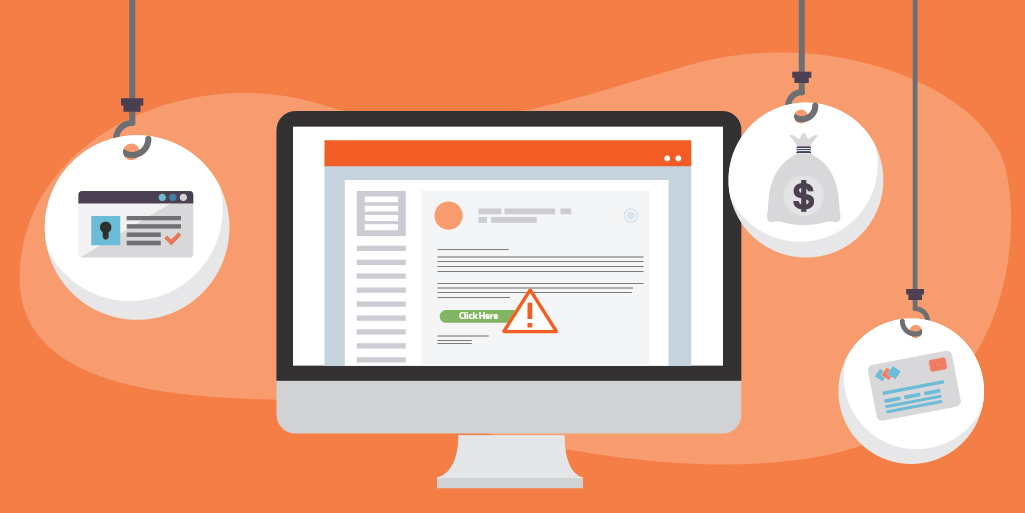
Beware of the 'ishing'
Social Engineering is the use of deception in order to manipulate the victim into performing an action for fraudulent purposes. The bad actor...

CIS Critical Controls Version 8.1
The Center for Internet Security (CIS) has long been respected for it's framework of critical security controls. Released in 2008, it's purpose was...

Data Privacy Day - January 28, 2025: You Have the Power to Take Charge of Your Data
As more data is stored in the cloud or transferred to third parties, how can...

Incident Reporting: Your First Line of Defense
Organizations use layered security to prevent falling victim to a cybersecurity incident. The 3 main elements of layered security require administrative, physical and...

Ring in the New Year with a Cybersecurity Makeover
A new year brings new opportunities. What a great time to review your cybersecurity practices! Evaluate every aspect of your digital life. Check...

Caught in the Web: Common Cyber Crimes
Cyber crime is a broad term that can encompass a wide variety of malicious activity. These attacks can be aimed at networks, businesses...

Salt Typhoon Cyber Attack
The Salt Typhoon cyber attack, conducted by bad actors in China, targeted telecommunication organizations. Major telecom companies were hacked, including AT&T, Verizon, T-Mobile...

'Tis the Season for Holiday Scams
Scammers are especially active during the holiday season. The crooks are taking advantage of the consumer's good cheer, generous nature, and hunt for...

Legislation to Protect Kids Online
The Children's Online Privacy Protection Act (COPPA) became effective on April 21, 2000. The act is designed to protect children under age 13...

Tabletop Triumph
Mastering incident response though simulation can assist with strengthening your plan. Once an incident response plan (IRP) is written, it does not prove...

How to Combat Administrative Sprawl
Administrative sprawl refers to the granting of unnecessary administrative permissions to resources. Many times there are controls put in place for granting elevated...

Cybersecurity Awareness Month -That's a Wrap!
As Cybersecurity Awareness Month comes to a close it is important to continue to exercise best practices throughout the year. Each October is...

CSAM - Update Software
October is Cybersecurity Awareness Month (CSAM) and is dedicated to raise awareness about the importance of cybersecurity. With the theme, 'Secure Our World',...

CSAM - Recognize and Report Phishing
October is Cybersecurity Awareness Month (CSAM) and is dedicated to raise awareness about the importance of cybersecurity. With the theme, 'Secure Our World',...

