In the world of cybersecurity, a Distributed Denial-of-Service (DDoS) attack is the digital equivalent of a massive traffic jam that blocks every road in and out of your network. Attackers might be hacktivists pushing a cause, cybercriminals seeking chaos, or even students trying to avoid an exam—but the goal is always the same: disrupt service and cause downtime.
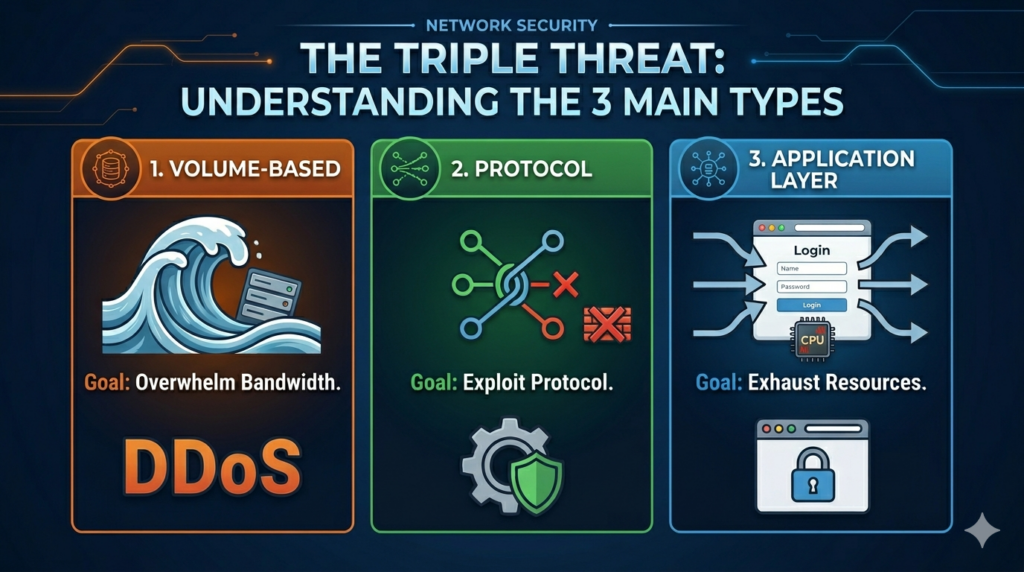
Recent incidents highlight the need to understand the three primary types of modern DDoS attacks—Volumetric, Protocol, and Application Layer—each designed to overwhelm systems in unique ways.
Volumetric Attacks (Layer 3)
The easiest to detect, volumetric attacks are the brute force of the DDoS world. The attacker’s objective is simple: send so much data to your network that the “pipe” becomes completely clogged, preventing legitimate traffic from getting through. These floods are measured in bits, gigabits, or even terabits per second. A common example is the DNS Amplification Attack. In this method, the attacker sends small requests to a public DNS server but spoofs the return address so that the responses are sent to the victim instead. Each answer from the DNS server is much larger than the original request, magnifying the impact. Multiply this process thousands of times, and the result is enough data to overwhelm your network connection.
Protocol Attacks (Layer 4)
Unlike volumetric attacks, which depend on sheer volume, protocol attacks exploit how systems manage network connections. Targets include the transport and network layers of the TCP/IP stack, particularly the processes that control connection states and resource allocation. A classic example is the SYN Flood.
When a legitimate client wants to connect to a server, it sends a SYN (synchronize) packet. The server replies with a SYN-ACK, waiting for an ACK in return to confirm the connection. In a SYN flood, the attacker sends streams of SYN packets but never completes the handshake. The server keeps those “half-open” connections in memory until it runs out of space, eventually denying new sessions—even from real users.
These attacks don’t require huge amounts of bandwidth but can still knock out routers, firewalls, and load balancers by consuming all available session resources.
Application Layer Attacks (Layer 7)
The most sophisticated and hardest to detect, Application Layer attacks target the topmost layer—where users interact with services like websites and APIs. These attacks appear to be legitimate traffic but target resource-heavy functions to overload the application itself.
A common example is the HTTP Flood.
Bots or compromised clients send thousands of legitimate-looking requests to resource-intensive pages such as search or login functions. Each request forces the server to use valuable CPU and memory, eventually exhausting them. Another variant, Slowloris, opens multiple simultaneous connections and sends partial HTTP requests very slowly. Because the server never receives a finished request, it holds the connection open indefinitely, tying up its worker threads until it can no longer serve new users.
Multi-Vector Attacks
Modern attackers rarely rely on a single method. Multi-vector attacks combine multiple DDoS techniques—Volumetric, Protocol, and Application Layer attacks—executed simultaneously or in sequence.
For example, attackers might begin with a UDP flood to saturate bandwidth and clog monitoring tools, while a quieter Slowloris attack drains application resources in the background. This one-two punch makes mitigation harder, forcing defenders to respond across multiple network layers at once.
Effective defense against these attacks requires visibility, layered protections, and automation. Relying on bandwidth alone is no longer enough.
Defense and Mitigation
So how can organizations protect themselves?
- Increase bandwidth: Expanding your internet connection can help absorb large volumetric floods, but it won’t stop protocol or application-based attacks. In many cases, the bigger the pipe, the bigger the attack.
- Use behavioral analysis and traffic scrubbing: Web Application Firewalls (WAFs) and dedicated scrubbing services identify abnormal traffic patterns, filter out malicious packets, and pass through only clean traffic.
- Maintain solid endpoint security: Every compromised device adds to someone’s botnet. Regular antivirus updates, Endpoint Detection and Response (EDR) tools, and strict firewall and email controls help minimize risk.
Organizations connected to MOREnet benefit from advanced DDoS detection and scrubbing services capable of identifying and mitigating even the stealthiest attacks.
If you suspect a DDoS event, contact MOREnet Support immediately—early detection and rapid response can make all the difference.
